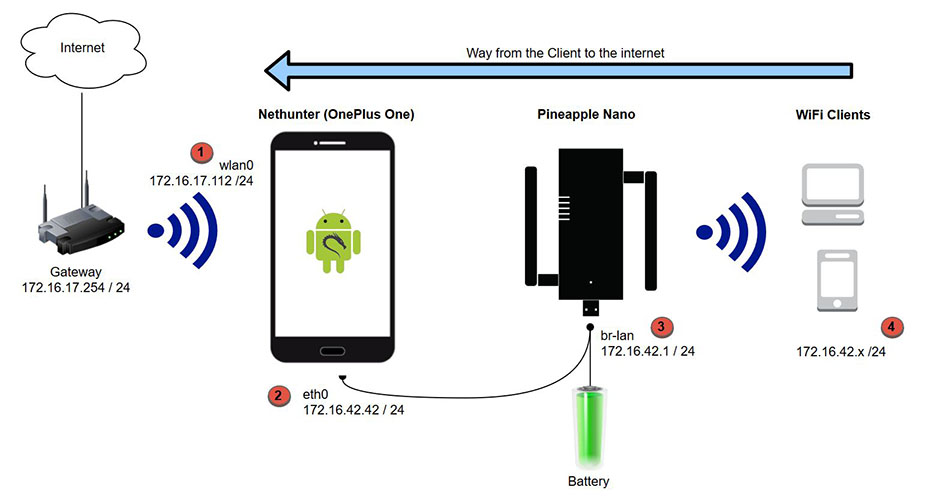
Here are the needed interfaces and routes shwon in the graphic:
Point 1 (Nethunter built in WiFi)
Interface wlan0
Code:
wlan0 Link encap:Ethernet HWaddr c0:ee:fb:27:35:cc
inet addr:172.16.17.112 Bcast:172.16.17.255 Mask:255.255.255.0
inet6 addr: 2003:85:ae45:60f1:54b5:4805:88ea:f458/64 Scope: Global
inet6 addr: 2003:85:ae45:60f1:c2ee:fbff:fe27:35cc/64 Scope: Global
inet6 addr: fe80::c2ee:fbff:fe27:35cc/64 Scope: Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:13344 errors:0 dropped:3383 overruns:0 frame:0
TX packets:5908 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:2336945 TX bytes:1047648
# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 172.16.17.254 0.0.0.0 UG 0 0 0 wlan0
172.16.17.0 0.0.0.0 255.255.255.0 U 0 0 0 wlan0
172.16.42.0 0.0.0.0 255.255.255.0 U 0 0 0 eth0
Point 2 (Pineapple/Nethunter eth0)
Interface eth0
Code:
eth0 Link encap:Ethernet HWaddr 00:c0:ca:90:d3:65
inet addr:172.16.42.42 Bcast:0.0.0.0 Mask:255.255.255.0
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:981 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:47306 TX bytes:34478
# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 172.16.17.254 0.0.0.0 UG 0 0 0 wlan0
172.16.17.0 0.0.0.0 255.255.255.0 U 0 0 0 wlan0
172.16.42.0 0.0.0.0 255.255.255.0 U 0 0 0 eth0
Point 3 (Pineapple)
Interface br-lan
Code:
br-lan Link encap:Ethernet HWaddr 00:C0:CA:90:BD:9C
inet addr:172.16.42.1 Bcast:172.16.42.255 Mask:255.255.255.0
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:1279 errors:0 dropped:0 overruns:0 frame:0
TX packets:3944 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:132027 (128.9 KiB) TX bytes:193882 (189.3 KiB)
# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 172.16.42.42 0.0.0.0 UG 0 0 0 br-lan
172.16.42.0 0.0.0.0 255.255.255.0 U 0 0 0 br-lan
Point 4 (Client)
Interface wlan0
Code:
wlan0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 172.16.42.167 netmask 255.255.255.0 broadcast 172.16.42.255
inet6 fe80::dc5c:d1e7:a60f:19cd prefixlen 64 scopeid 0x20<link>
ether 00:25:d3:5a:d4:7f txqueuelen 1000 (Ethernet)
RX packets 1220 bytes 108079 (105.5 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 118 bytes 21822 (21.3 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
# route -n
Kernel-IP-Routentabelle
Ziel Router Genmask Flags Metric Ref Use Iface
0.0.0.0 172.16.42.1 0.0.0.0 UG 600 0 0 wlan0
172.16.42.0 0.0.0.0 255.255.255.0 U 600 0 0 wlan0
traceroute google.com
traceroute to google.com (172.217.21.206), 30 hops max, 60 byte packets
1 Pineapple.lan (172.16.42.1) 1.373 ms 1.717 ms 2.084 ms
2 172.16.42.42 (172.16.42.42) 5.044 ms 5.542 ms 5.519 ms
3 172.16.17.254 (172.16.17.254) 6.803 ms 7.683 ms 7.665 ms
4 192.168.217.1 (192.168.217.1) 7.642 ms 8.338 ms 8.319 ms
5 217.0.119.62 (217.0.119.62) 24.563 ms 27.663 ms 27.603 ms
6 87.190.164.162 (87.190.164.162) 32.795 ms 24.875 ms 21.212 ms
7 217.239.41.222 (217.239.41.222) 23.999 ms 217.239.49.142 (217.239.49.142) 23.987 ms 217.239.41.102 (217.239.41.102) 25.673 ms
8 74.125.50.149 (74.125.50.149) 26.854 ms 29.469 ms 30.530 ms
9 66.249.94.88 (66.249.94.88) 80.414 ms 66.249.94.86 (66.249.94.86) 30.485 ms 30.416 ms
10 209.85.142.17 (209.85.142.17) 31.286 ms 24.597 ms 23.724 ms
11 216.239.40.6 (216.239.40.6) 32.221 ms 32.199 ms 32.121 ms
12 209.85.247.100 (209.85.247.100) 33.281 ms 209.85.247.82 (209.85.247.82) 33.936 ms 216.239.57.191 (216.239.57.191) 33.919 ms
13 72.14.232.177 (72.14.232.177) 33.850 ms 216.239.47.59 (216.239.47.59) 33.829 ms 34.791 ms
14 108.170.235.247 (108.170.235.247) 35.872 ms 35.853 ms 108.170.235.245 (108.170.235.245) 35.785 ms
15 fra16s12-in-f14.1e100.net (172.217.21.206) 37.422 ms 37.405 ms 37.339 ms
I want to build the same setup as Simone Margaritelli (evilsocket) but with the Nethunter device instead of the Mac --> https://www.evilsocket.net/2016/09/1...tterCap-setup/
Seems to me that i´m missing a point or that i need to NAT on another interface instead only eth0 on the nethunter device ?
Simone did the NAT rules on the pineapple itself - what i already tested without luck. Same behaviour.
Here are my use rules:
Code:
root@Pineapple:~# uci get network.lan.gateway
172.16.42.42
root@Pineapple:~# iptables -t nat -A PREROUTING -p tcp --dport 80 -j DNAT --to-destination $(uci get network.lan.gateway):8080
root@Pineapple:~# iptables -t nat -A PREROUTING -p tcp --dport 443 -j DNAT --to-destination $(uci get network.lan.gateway):8083
root@Pineapple:~# iptables -t nat -A POSTROUTING -j MASQUERADE
root@Pineapple:~#
What have i done so far?
1.) Open a ANDROIDSU Shell on the Nethunter device. I start the Nethunter Pineapple Connector manual because the GUI has a small bug (https://github.com/offensive-securit...ter/issues/598)
2.) # cd /data/data/com.offsec.nethunter/files/scripts
3.) # ./pine-nano start 172.16.42.42/24 172.16.42.0/24 172.16.42.1 1471 start_proxy
4.) Check iptables for the port redirection:
Code:
# iptables -vnL -t nat
Chain PREROUTING (policy ACCEPT 9 packets, 1086 bytes)
pkts bytes target prot opt in out source destination
0 0 REDIRECT tcp -- eth0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:80 redir ports 8080
0 0 REDIRECT tcp -- eth0 * 0.0.0.0/0 0.0.0.0/0 tcp dpt:443 redir ports 8083
Chain INPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 2 packets, 143 bytes)
pkts bytes target prot opt in out source destination
Chain POSTROUTING (policy ACCEPT 1 packets, 60 bytes)
pkts bytes target prot opt in out source destination
16 1167 MASQUERADE all -- * wlan0 0.0.0.0/0 0.0.0.0/0
Chain natctrl_nat_POSTROUTING (0 references)
pkts bytes target prot opt in out source destination
Chain oem_nat_pre (0 references)
pkts bytes target prot opt in out source destination
How can i get bettercap working correct ?
I´v tested it with NAT on the pineapple as Simone did and i tested the pine-nano script with and without the "start_proxy" option that set these rules:
Code:
f_transproxy(){
# For Bettercap/mitmproxy which acts as a transparent proxy
iptables -t nat -A PREROUTING -i eth0 -p tcp --destination-port 80 -j REDIRECT --to-port 8080
iptables -t nat -A PREROUTING -i eth0 -p tcp --destination-port 443 -j REDIRECT --to-port 8083
}
In any case - bettercap doesn´t work correct and i don´t find my error in the setup.
Thanks for any hint/help!
Greez
BeNe




 Reply With Quote
Reply With Quote